Every device gets its own
isolated network.
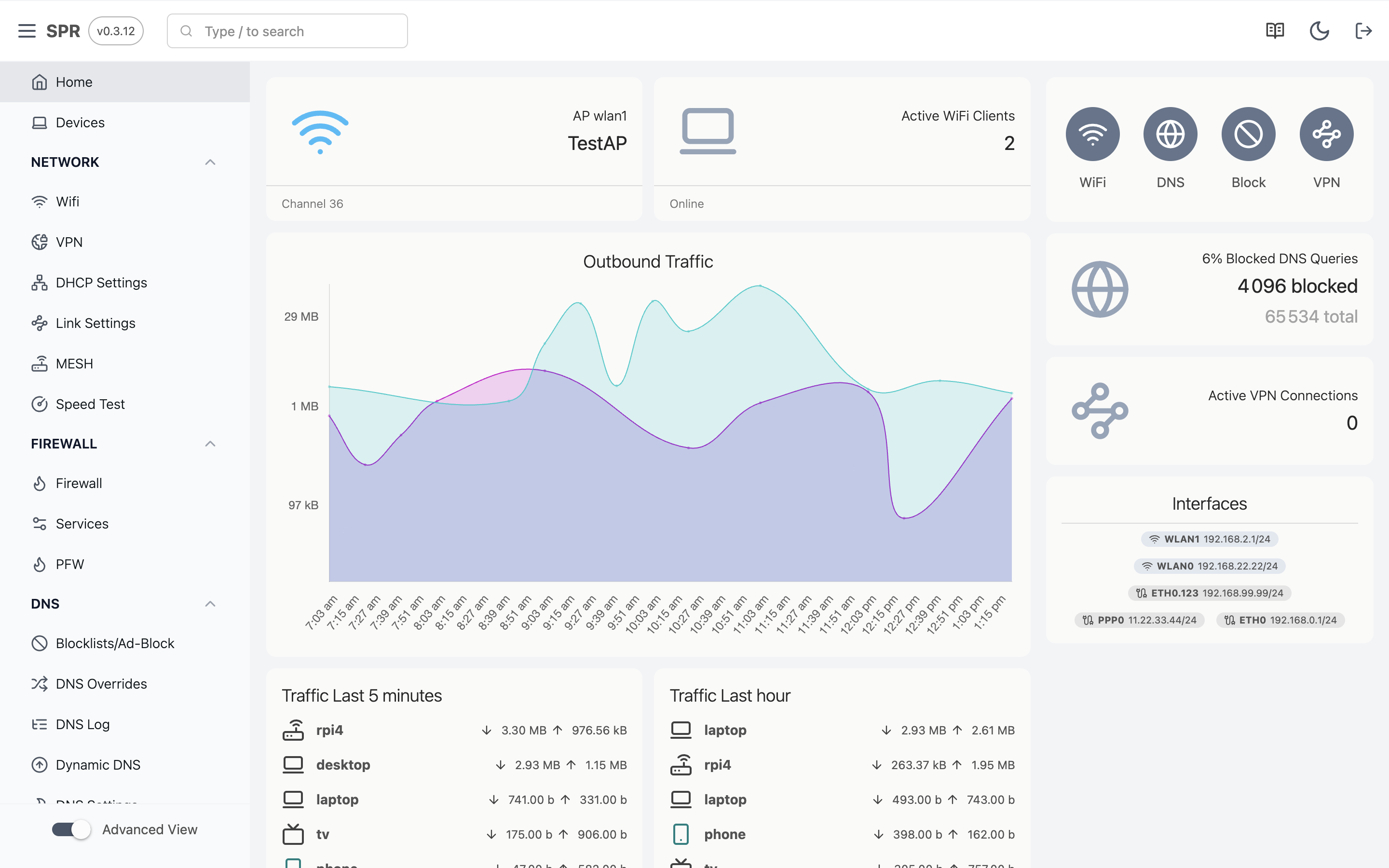
SPR places each WiFi device into its own VLAN with a unique password and a default-deny firewall policy. Devices are isolated from each other by default. You write policies using device names, and SPR handles the IPs and VLAN tags underneath. Anything you haven't permitted stays blocked.